You may never know how serious online security and identity theft is until you fall victim to one of these fraudsters. Imagine one day you get a call from your bank about an unpaid $10 000 credit card charge that you have no idea about, or in a more extreme scenario, the cops bust down your front door, arrest you and accuse you of money laundering (this may be going over the edge, but it happens!). No one is beyond the reach of identity thieves, from top celebrities to everyday individuals.
Everyone with a bank account is a potential victim of cybercrime. Maybe you have heard about the case of Carlos Lomax, who stole the identity of Will Smith, opened 14 credit cards, and racked up a balance of $34,000 in his victim’s name. In 2013, Kim Kardashian wasn’t spared, as Luis Flores stole Kim’s identity and transferred over $71,000 from Kris Jenner’s account to his account. Other victims of his scheme were Tom Cruise, Ashton Kutcher, and Paris Hilton. It may interest you that Luis also had the SSN and bank information of Beyoncé, Michelle Obama, and Bill Gates.
The internet is laced with countless cases of identity theft. You have criminals hiding behind fake usernames and pretending to be people they are not. And here’s what you need to know: it is easy for people to search and find your personal information online. With only a few keystrokes and malicious intentions, an identity thief can find your name, address, and phone number. Someone who knows where to look can find even your mother’s maiden name, your SSN, and your security passwords. Your information is not safe online.
Usersearch.org is a website that you can use to check the Internet to see if any unauthorized person is using your information. Searching Usersearch.org can quickly alert you to any suspicious accounts that may be someone’s attempt to clone your information. Simply visit Usersearch.org and type in a username that you use regularly online. For this example, I used a random name, “Caroline.” Click on search.
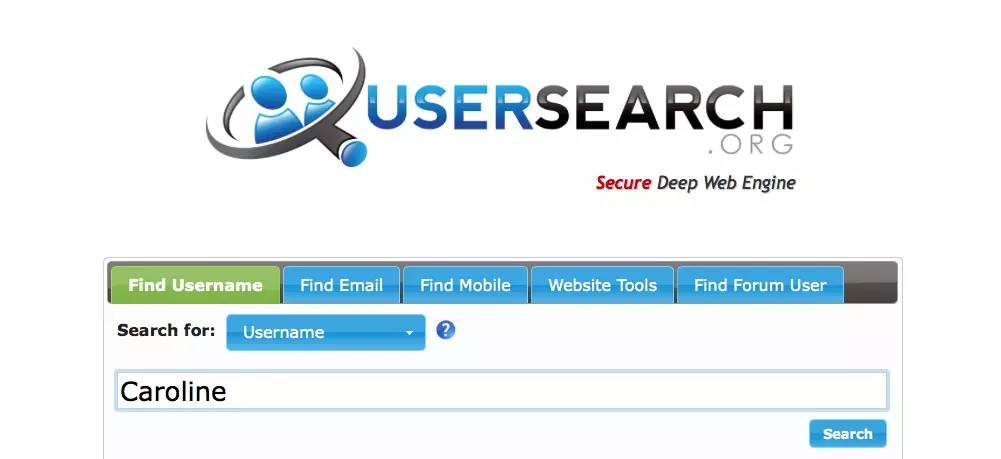
As you can see, there’s an option to search for usernames, emails, mobiles, and website tools (locate a company owner using their IP address). Searching for a specific username, email address, or mobile number will show you all the different places online where your search term can be found, and the website’s tools search option can be used to find detailed information by entering an IP address. The “find forum user” option is still under construction. The Username.org search results let you see and verify that your information is being used only in places you know about. Now let’s go back to our search for the username “Caroline”….
Wait for it…
There were about 23 search results. Here are some of them:

You can see that the search results show several different social media platforms where the username “Caroline” is being used. I took it further by clicking on Caroline’s Twitter handle, and boom!… I was able to see ‘Caroline’s Twitter profile just like that. The search actually works.
Let’s look at this critically and assume I am an identity thief.
First, I search for a promising username. Next, I look through their social media and see what they post about. What they are saying and who they are following. I will also download their images. And finally, I will create a profile using a similar name and send requests to their friends. With this, the ball has been set in motion to perform fraudulent activities such as scamming people, asking for money, and performing other heinous crimes under the guise of someone else.
Don’t be fooled by thinking that cybercrime is a crime is purely a technical problem with a technical solution. An anti-virus or firewall may be effective when protecting your computer, but there’s very little they can do to keep your online identity safe. So next time someone talks about online security, you should realize that you are not as safe as you think. The Internet is filled with trails of your activities, and you may be the next victim of an identity thief. Don’t be a victim – check Usersearch.org regularly to ensure your information is not being used without your consent.