What are the top 17, Open Source Tools (OSINT) to find anyone online? What a great question! and a huge one.

Here are the top Open Source Tools, we believe:
- Maltego
- UserSearch.org
- DorkSearch
- ScamSearch
- Mitaka
- SpiderFoot
- Spyse
- BuiltWith
- Intelligence X
- DarkSearch.io
- Grep.app
- Recon-ng
- theHarvester
- Shodan
- Metagoofil
- Searchcode
- SpiderFoot
- Babel X
- ChatGPT
In this article, we spend time talking to OSINT experts and private investigators to find out. Here we cover their good and bad points (not many bad points!), giving our review, link, and advice, for 2022.
What’s in it for you?
This document will increase your knowledge and add 16 amazing investigation tools, leading you deeper into the dark and quite often secret cave, of online investigations.
As I’m sure you know, Open Source Intelligence (OSINT) is the application of utilizing data that is publicly available, to achieve your aim.
Open source may give the impression of publicly available information only. OSINT could also utilize human intelligence (such as social engineering). But, there are many methods of gathering and sifting this intelligence, not all, but most, including using computer systems.

Why is OSINT so important?
OSINT is making sense of the chaos that is online data (and sometimes offline). Anyone can gather information, with the right tools. True OSINT is making the links between the information to achieve a goal. OSINT tools provide solutions, simple. Solutions, to make your life better.
Using OSINT tools for discover public-facing assets
One of the more common aspects of starting an OSINT gather is attempting to pinpoint public-facing assets, such as websites, company addresses, and personal addresses. We’re not really interested in system or computer program vulnerabilities, that’s more for the penetration testing world.
However, a little bit of penetration testing knowledge can glean some information. For e.g., by remotely connecting to a server system owned by your target, you can get some intel. Before you enter a username or password, you’re presented with the operating system and contact details of the administrator. Sometimes, this can be useful in social engineering situations.

Using OSINT to discover relevant information outside the organization
A secondary function of OSINT tools these days is to find ‘extra’ relevant information outside of the direct query that you have looked for. Such information could be an acquired company, a secondary company, or close relationships or contacts with the target in question. This can identify further potential physical address locations of the target. Other interests such as social network accounts and social life pictures, can provide a picture. That picture may show the local social habitat and the target. You may now be aware of their local stomping grounds online.
Collate discovered information into actionable form
Finally, once the information has been searched, and collected, including the connected relevant information, someone needs to group this all together. They should be linking all the points together and apply some logical analysis (an investigative mindset required!).
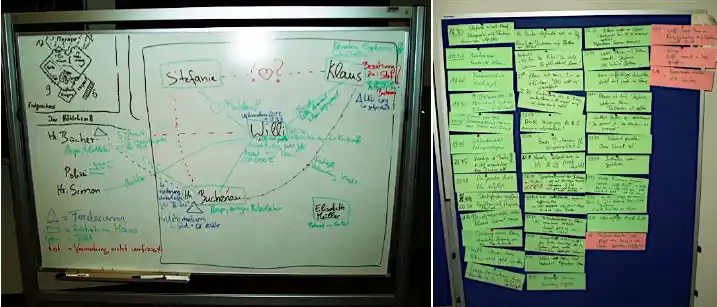
Running OSINT scans can return large volumes of information, you need to be well-versed in focusing your time on the information that matters, with a keen eye for detail. Piecing all that information together to focus on the most useful aspects can be very effective in painting the larger picture. Tools try to do this, but really, this part needs a good human brain and some coffee.
Top OSINT tools used by the Experts
The first job to do? choose the right tool(s!). You don’t need to use any tools, but given the vast locations where information can be, having a tool helps. A tool that checks thousands of locations within a few seconds can be very time-efficient.
If you’re trying to discover information on your own identity or business, preventing future online attackers, you want something quick and repeatable. Doing this quickly could mean the difference between your employees or family from receiving phishing attacks.
So, here you have it. The top tools we think will help you to conduct a thorough, and effective, OSINT analysis of either your target or your own assets. We list them here, then go into detail about how each one can make your investigative career, more effective (in no particular order):
- Maltego
- UserSearch.org
- DorkSearch
- ScamSearch
- Mitaka
- SpiderFoot
- Spyse
- BuiltWith
- Intelligence X
- DarkSearch.io
- Grep.app
- Recon-ng
- theHarvester
- Shodan
- Metagoofil
- Searchcode
- SpiderFoot
- Babel X
- ChatGPT
1) OSINT Tool: Maltego – making complex OSINT easy, with great maps and transforms
Maltego focuses on finding particular relationships between assets, people, companies, and website domains (and it does this very well). Most major OSINT platforms provide Maltego with an API, these days. They let the tool hook in and present the data in Maltego. However, it can be known to take a large amount of time to time to plot all the raw intelligence.
The graphs in the tool do an amazing job at presenting the information in easy-to-read charts. The latest we heard, it can show up to 10,000 data points.

The tool works by automating the search of your input, against various public information sources. It attempts to provide a 1 click source solution, and we think it does this very well. It manages these data sources by something they call a ‘transform’, and it comes with quite a few inbuilt features. Some of these are DNS records, social network searching, WHOIS checks, and a few others. You can also add custom transforms if you find a compatible API to hook up.
There is a free version with limited features and a charged instance of $1,999. They also provide server installation solutions for large-scale solutions, which start at $40,000 and include intensive training.
2) OSINT Tool: UserSearch – Finding people by usernames and Email
UserSearch is a vast network of search engines that crawl the web to find an exact match on a username or email address. It scans across hundreds and hundreds of websites. It can locate a particular user profile on Forums, Social networks, dating websites, message boards, crypto websites, and gambling websites. It’s by far one of the most comprehensive and accurate search engines online for usernames and email addresses. A popular feature of this site, is its ability to scan all the popular dating websites, for usernames. A nitfy tool for private investigators!
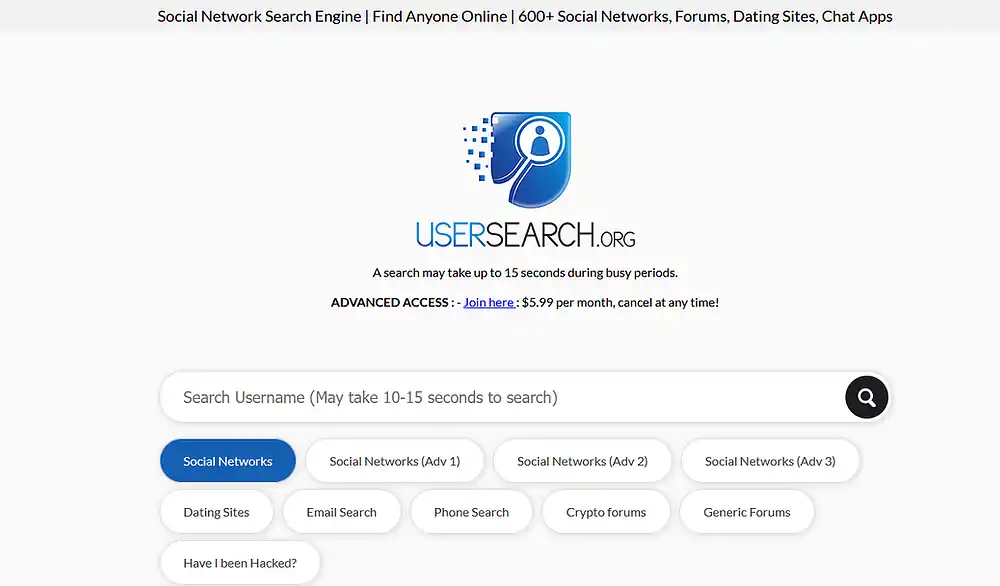
Its been running for over 15 years, so the developers have a pretty strong position for OSINT of usernames or email addresses. The developers are a team of open-source experts and software developers.
The site is totally free to use and it can check up to 800 sites within about 30 seconds, which is pretty amazing. It’s quite literally Google, for usernames and email addresses.
They also recently released a premium service that is in the Alpha version. It reports finding even more information and covers more websites, such as dating sites, within the premium version. They offer the service for $6.99 per month which you can cancel at any time.
3) OSINT Tool: DorkSearch – Google Dorking to the Extreme
Here we have DorkSearch.com, a free service created and released to the community in early 2022. The tool seems to be a variation of the service offered by exploit-DB but with far more useful and reaching capabilities.
New to OSINT? Dorking is basically a set of semi-secret search terms that can be used in Google. Using them can show results not really intended to be in Google! Also known as ‘Deep Web (not to be confused with Dark Net/TOR).
The developers have essentially created a Google, for Dorks. Here in the picture below, you can see they have an easy-click interface. It subsequently lets you browse what dork you are interested in, and then you just need to click what you want. No more typing in search terms and trying to work out what dash or exclamation mark you missed out!
They also created, what they call ‘Builder.’ This is a huge collection of Dork terms, but they include information such as purpose, tips, and whether they work on web/images/groups or newsgroups. What you can do is click a Dork, and that term gets auto-populated into their search bar. You can then click another Dork, and it gets appended to the search bar. It encourages users to discover totally brand-new Dork Search terms via a process of simple clicks. A great idea!
4) OSINT Tool: ScamSearch.io – A Global Database of individual scammers & scam websites
Another free service to come online during 2022 is ScamSearch.io. One of the biggest for the OSINT community to date we think. ScamSearch is a huge (huge!) database of crowd-sourced reports, of scammers. Crypto scams, email, social networks, offline scams, phone scams, literally every single scam situation you can think of; this site records it and makes it available for free. They currently have roughly 10 million recorded scammers and it grows weekly by several thousand.
They have a simple search bar that lets you search for the username, email, crypto address, nickname, real name, or website, across their database. Given the size of the database, you’d think the search would be slow…but it’s instant. Their search bar also drops down and offers suggestions similar to your search term, if they have something close.
ScamSearch, due to its crowdsourced nature, also encourages users to use its service to report scammers. A lot of OSINT researchers and anti-scam communities use this data to target scammers and hinder their work, so you’re doing good by reporting them here!
5) OSINT Tool: Mitaka – finding IPs, MD5s, ASNs, and bitcoin addresses
This is available as a Chrome Extension and also for Firefox. It allows you to search over a dozen major search engines for domains, URLs, IP addresses, MD5 hashes, ASNs, and Bitcoin addresses.
It’s a very handy set of tools in your browser, and for those who may prefer a more focused, limited set of tools.
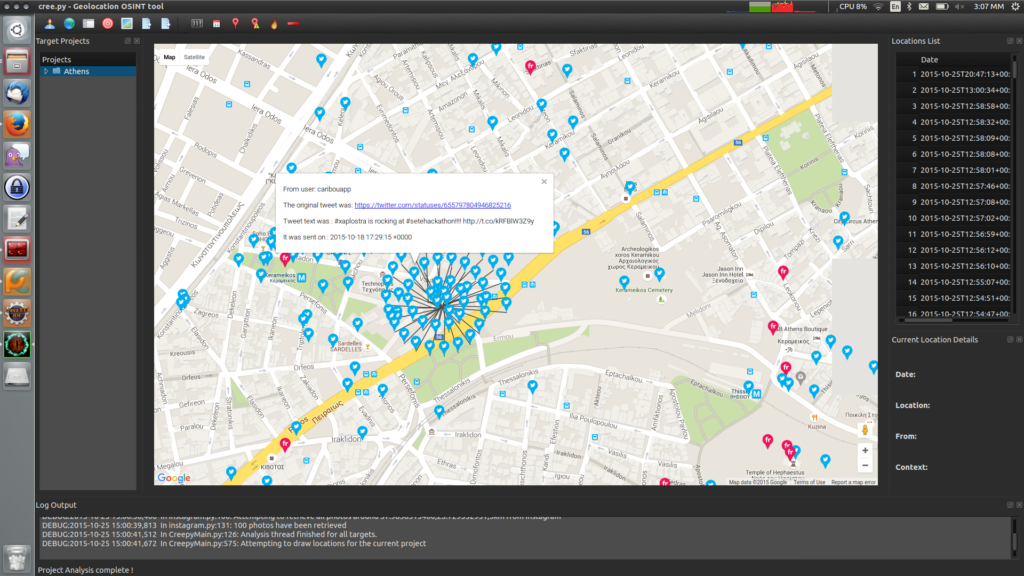
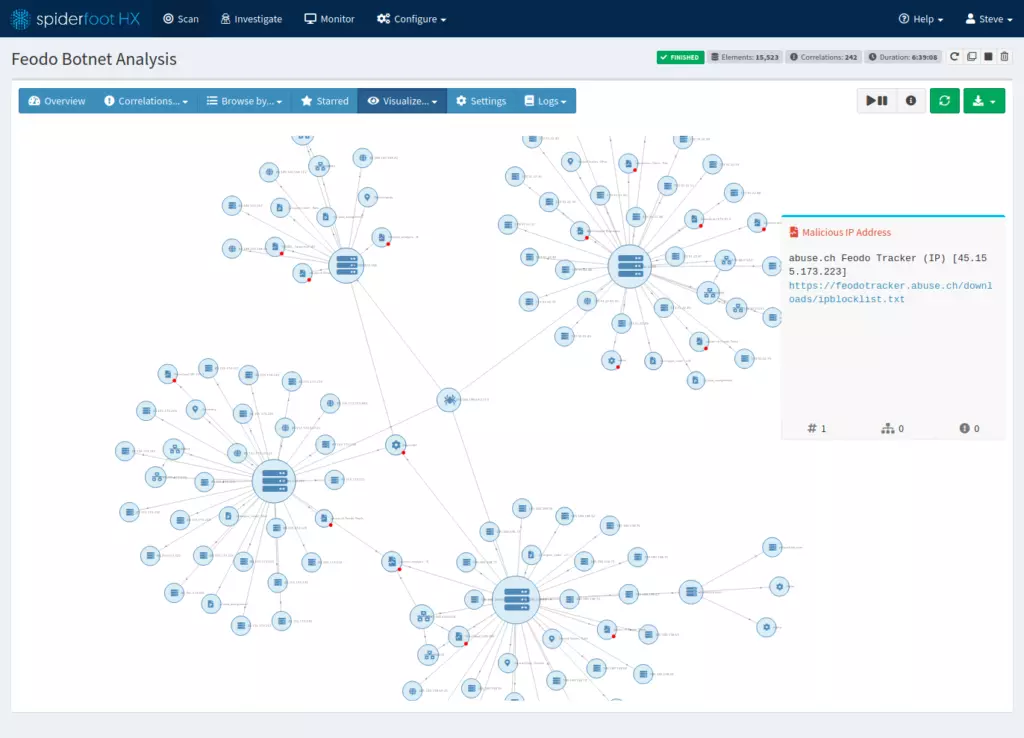
6) OSINT Tool: Spiderfoot – vast array of open source intelligence resources
This is a free recon tool that can pull data from multiple different sources to glean information on various online assets. It searches for IP addresses, CIDR ranges, domains, subdomains, ASNs, email addresses, and phone numbers. It’s on GitHub and comes in both a command-line version and an embedded web-server version. It contains over 200 modules, making it perfect for red and blue teams as part of your initial process.
7) OSINT Tool: Spyse – the OSINT goto tool for domains
This tool is described online as ‘the most complete internet asset registry‘ online. Its main focus seems to be leaning toward cyber security work. The tool is used by many major OSINT tools, providing the back-end data. It collects publicly available data on websites, and their WHOIS information (such as owners, associated servers, and IoT-linked devices).
The data can then be reviewed by their own engine to identify potential security risks and connections between various entities. It does have a free plan, although developers who hope to build applications from the data being provided by the Spyse API, will need to pay a subscription.
8) OSINT Tool: BuiltWith – OSINT to find what sites are built with!
Can you guess what this tool does? Using Builtiwth, you can determine what technology stacks are used on various websites and platforms. It can, as an example, detect whether a website is built using WordPress, Joomla, or any other CMS-like platform. It will also generate a great service list of the plug-ins that the website is currently using, its frameworks, and even its server information that’s publicly available. It’s another great tool for red and blue teams in initial server recon as part of a security audit.
As an additional bonus, you can link this tool in with a security scanner, such as WPScan, and the WordPress Vulnerability Database API. This can then quickly spot common vulnerabilities within the WordPress modules being used.
9) OSINT Tool: Intelligence X – a database of literally everything OSINT!
Intelligence x is one of the best archival services and search services that we have to access online. Not only does it archive historic versions of websites online but it also includes leaked data that is typically removed quite quickly these days. Although this may sound a little similar to what Internet Archive’s service offers, Intelligence X offers some pretty cool differences. No matter how controversial the data leak, Intelligence X seems to not worry too much, providing it public for the masses, forever.
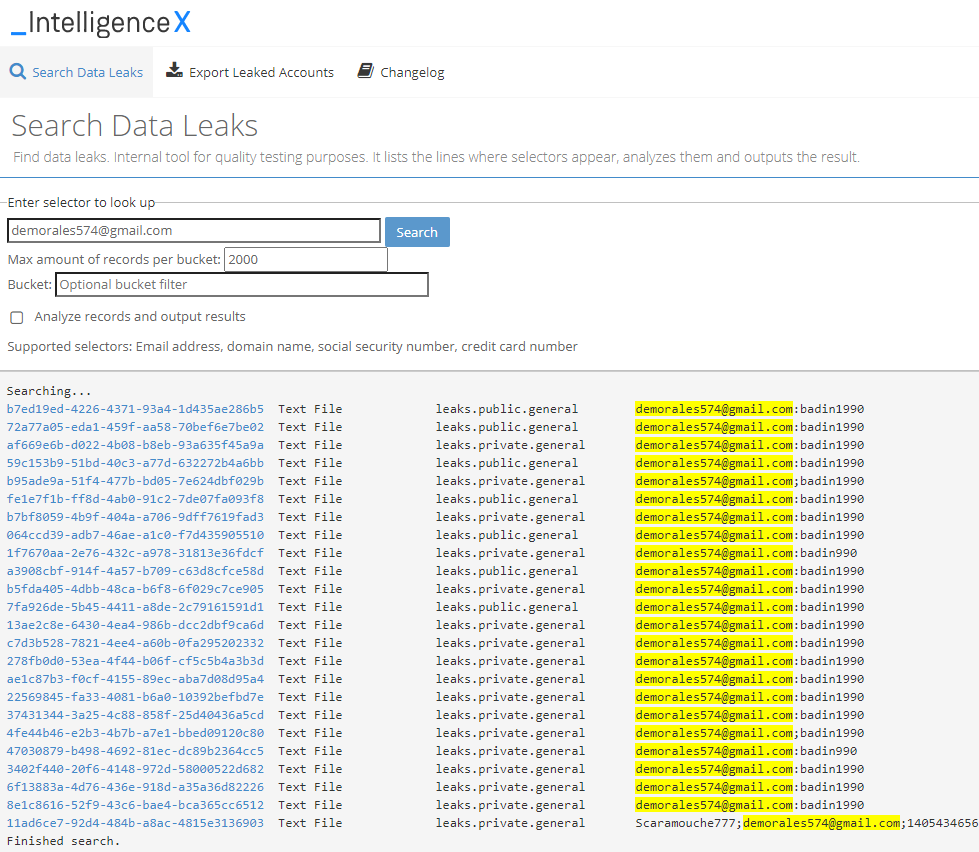
Previously, its archived information such as the email servers during the leak of the Hillary Clinton and Donald Trump situations.
10) OSINT Tool: Grep.app
Ever thought that if you could search across half a million git repos with a couple of clicks, would be handy? sure you may have tried using the search bar on Github. But, Grep.app does the job far quicker, and more effectively.
11) OSINT Tool: Recon-ng – great for python scripters
Do you have a little bit of Python coding? If so, you have an early Xmas present when it comes to recon-ng. This is a very powerful python tool, which is written in python. It allows you to interface very nicely with Metasploit Framework, which should make matters easier for you to learn its uses. It also has a help area that guides you on the best uses of the tool, so python developers should be able to integrate it pretty quickly.
The tool itself automates one of the most time-consuming aspects of OSINT actions. It allows you to automate more of the time-consuming repetitive actions, allowing you to focus on the actual OSINT investigation.
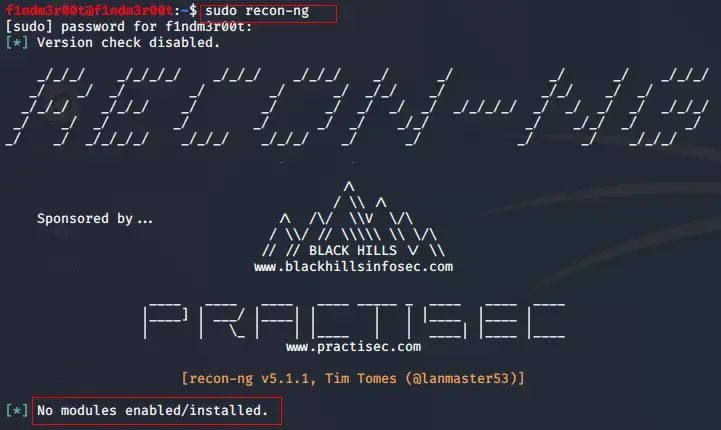
It’s designed so even the newest python developer should be able to utilize the tool to search public information and return some decent results. It works in modules, with a lot of inbuilt functionality designed for easy use. Common tasks such as normalizing the data outputs, linking into databases and making URL requests to websites, and using/managing API keys to gather data directly from API interfaces, are fast and easy to do with Python. Instead of needing to program Recon-ng, it allows you to simply choose what module you want to use and give it the destination.
The tool is free and open-source and it includes a huge wiki that comprehensively includes information on how to get started and used the tool, using best practices for OSINT.
12) theHarvester – OSINT for networks
One of the easier tools to use out of the box that we’ve come across is the popular tool theHarvester. It’s built from the bottom up to gather public information that exists in an organization, but outside the organization’s own network. It can identify interesting public information on an organization’s computer network, by looking outside the fence. Using a multitude of inbuilt tools to do this, makes it a very effective reconnaissance tool prior to starting a penetration test or a similar activity.
The tool gathers information from major data providers such as Bing and Google but also uses less-known areas of the web and meta engines.
To do this it hooks into Netcraft for data mining and the Alien vault threat exchange, allowing it to quickly identify known vulnerabilities. In basic, it can port scan, and gather emails, names, subdomains, IPs, and URLs on an organization, perfectly positioning you for the next steps of you’re exercising.
13) OSINT Tool: Shodan – the Google for IoT devices
Shodan is an amazing, used to find intelligence on IoT devices. Why? this kind of data is not normally searchable, so you’ll be surprised at what you can find out.
It can detect open ports, and vulnerabilities on targeted systems, and scan devices that are not typically supported by standard port scanners.
Other OSINT tools, like theHarvester, actually use Shodan as a data source for detecting vulnerabilities on IoT devices. One of the greatest advantages of Shodan is its to purely monitors so many hundreds of thousands of IoT devices and the information it contains on these devices, making it publicly available. If you don’t use this tool at the start of an OSINT, you’re missing a huge amount of data. Devices such as cameras, building sensors, security devices, Xboxes, security cameras, and household fridges! The list is endless.
This tool is a charged service, but well worth the cost. It costs $59 per month at basic. But to test it out, you can register a freelancer license and scan up to 5120 IPs per month for free.
14) OSINT Tool: Metagoofil – who made that document?
This is a freely available tool on Github. It’s been designed and optimized to pull out information and metadata on public documents, such as PDF, Doc, Docx, Xls, and other common document formats. It’s literally an online, document investigation tool.
The kind of information you can pull from this tool is very interesting and impressive. It can return artifacts such as the username of who created the document, as well as their real name and sometimes their address (if the computer used to create the document contains the registered system details containing this information). Also artifacts such as server name, network share resources, and directory information of the network shares.
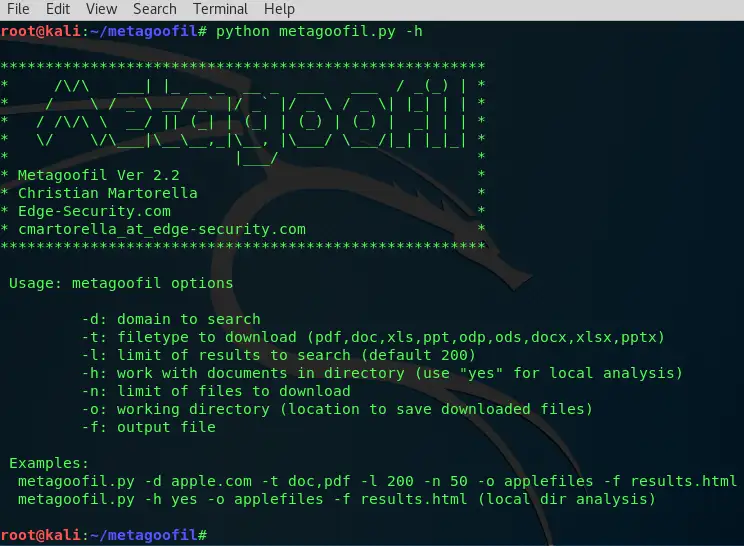
It goes without saying, this kind of data leakage from an organization is very useful for anyone who works in the OSINT field, or perhaps needs to conduct some social engineering activities. A very valuable and free resource for any OSINT investigator.
15) OSINT Tool: Searchcode – the Google of code!
Search code is essentially the Google equivalent of software code. Software developers quite often leave sensitive information within the source code of computer programs, on the assumption no one will ever look. You can come across emails, usernames, and even passwords inside the source code. This tool searches the source code, quickly finding useful forgotten pieces.
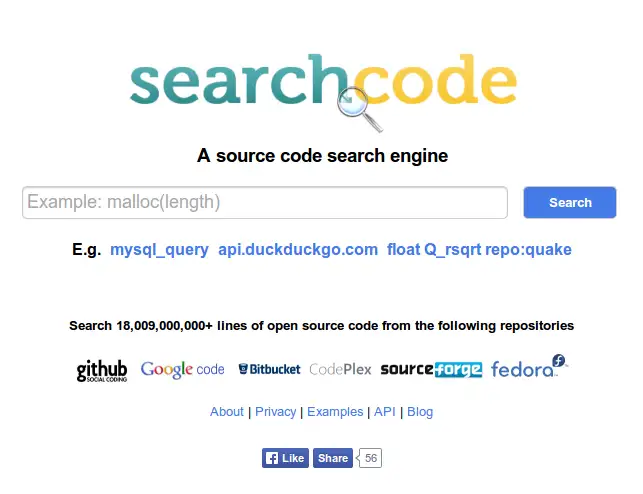
You don’t need to be a developer or coder to understand the results of this search engine, and most of the time the results are self-explanatory. Another great resource for OSINT investigators where they know their targets or organizations may have released software.
16) OSINT Tool: Babel X – Open source intelligence in Chinese, Russian, Tamil…
Do you ever need to conduct an OSINT investigation on a target and they may speak another language, but you don’t? This could be a problem. From our research, about a quarter of internet users worldwide speaks English as their first language, although some sources say it’s 55%. What about all that useful information that we can’t see if were not fluent in Spanish, Chinese, Russian, or Tamil?
This tool is the solution to that problem. It lets you search the public web, such as blogs, social media, and common message boards, plus the dark web and deep web. It can currently search against data sources from more than 200 languages.
This is a hugely useful resource, and OSINT investigators should definitely try this out.
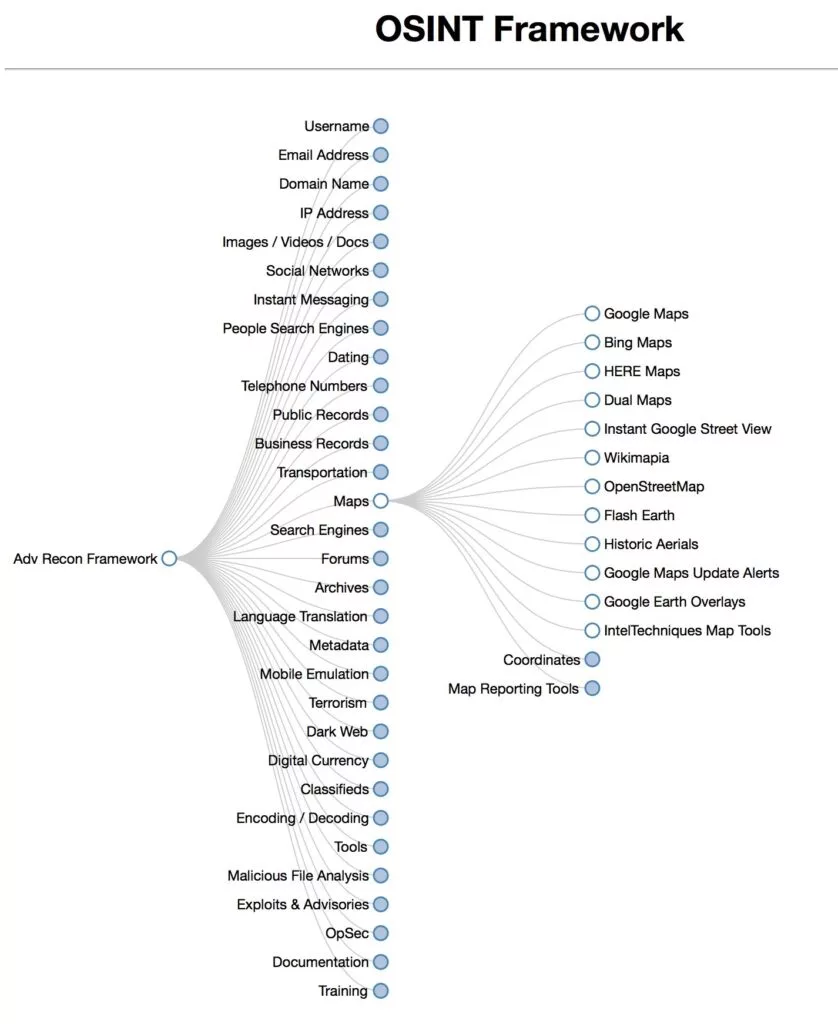
17) OSINT Framework Resource – The Best of the best
All in all, what is the best resource online?
The OSINT Framework resource. Why? It’s an amazing resource to see far more online resources for OSINT. It’s very, very, popular. OSINT Framework website has a huge array of OSINT resources for all walks of life.
Bonus OSINT Tool for 2023 : AI for OSINT
The latest addition to the best OSINT tools for 2023, which may not initially come across as an osint tool, is the one and only…ChatGPT!
What can it do for me, we hear you saying? You can:
- Create a Google Dork query, from a description (i.e., “give me a google dork to find SQL databases for UserSearch”).
- Searching databases on sites such as Match.com, to work out if an email is registered on that site.
- Give you investigative ideas for you to progress, from a description of your investigation.
- Summerise an investigative result into a simple paragraph, for your clients.
- Translate text to another language, perfectly.
- Give it a case, and let it identify any commonalities between them.
- The list is unlimited (ask it how it can help you with an OSINT investigation!)
The new age is here, and it’s very exciting.
Best of the best open-source intelligence tools!
So, in finality, we believe the OSINT Framework is the single most useful resource online. It’s one of the best locations to find what you’re looking for. We suggest you give it a try and explore what it has to offer.
We do think what we’ve listed is quite simply the best of the best current online. If you are an OSINT or information professional, having all these tools in your shortcuts will pay off. You don’t need to be a uber technical person to be able to use them, and with a decent head on your shoulders, you’ll find what you’re looking for. Feel free to contact us if you have any good resources and we’ll be happy to talk about them in the next article.
Next, read this: