To quickly do a user lookup to find someone online, on social networks, or on dating sites with just a username or email address, you can:
- Use a reverse lookup tool to find them, if you have their username or email address.
- Manually visit the websites themselves and utilize the inbuilt search functions of the website.
- Add some of their friends as your friends and you may be able to see their profiles then.
- Search google cache for the specific site, for example, “site:match.com fred@hotmail.com”.
- Try a more generic people search tool, such as Pipl.
- Access the website’s public API and perform the search directly.
- Read this article and find out how to do all these, with and without tools.
If you’re searching the web, wondering how to find your ex, long lost school friend, or future date, you may come across words in google such as reverse image search, reverse user search, user lookup tool, background check, etc.

Fed up with the same old…
All these terms will bring you the same place, which is, where can I find a big bunch of data that will let you search? 95% of the time you’ll have an article wasting your time, and 4% of the time you’ll be forwarded to a user lookup page that will charge you. Frustrating we know. You may prefer to do this yourself, rather than relying on a tool, which we can totally understand.
This article will show you exactly how to do these user lookups yourself, using just your patience, determination, and your brain. We’ve been doing this for decades, and we automated the process into our search engine, but we want to show you how to do it without using any tools.
Finding users on the following Social Networks
During this article, we are actually going to walk through a number of websites, manually, and show you exactly what you can, and cannot currently see from a public-facing, non-registered user account on the following websites (by popular demand):
- POF (Plenty of Fish)
- Match Dating site (match.com)
- Cash App
- Kik Messenger
- Xbox Live
- Minecraft
- Github
- Snapchat
- Onlyfans
- Tiktok
We are a team of cyber enthusiasts, computer programmers, open-source experts, and web crawler, developers. The fields of specialism include building web crawlers to gather public information and then providing that data onto websites (our website). Our combined knowledge consists of decades, and our wrinkles show.
Manual, you say?
While we are manually going through these 11 sites, rest assured that we are testing all the usual tricks. These include fake data submissions, URL path analysis, API checks, reviewing the Java script of each site, and checking if there are hidden APIs we can access. We’re reviewing the form structure of the sites to determine if additional information can be gleaned publicly, checking where the data is going, and testing if we can send our own data without authentication. We are not hacking, we’re simply checking if there are public bits of information that are not publicly advertised.
We will tell you what worked, and what did not work. If nothing else, this article will aid your own research in knowing what not to bother trying and hopefully aid you in developing your own personal strategy in conducting user lookups online.
How to conduct email and user lookups
Whether you’re using automated lookup tools or manually investigating a target, the methodology is rather similar. You need a lot of patience, determination, and knowledge of what you’re looking for. Websites, generally, unless purposefully designed to be as public as possible (such as Reddit minus the email), do not openly advertise the personal information of people under usernames and email address accounts. Quite often, the knowledge that a username or email is actually active on a particular social network or dating site, or at least has been active, are an indicative indicator and positive result as a part of an OSINT investigation or personal mission to lookup someone online.

Negative confirmation?
Sometimes, having a positive or negative confirmation that a user or email address on a particular website is all you going to get (and sometimes that’s all you need!). By utilizing the information we pass onto you in the following few pages, in combination with the guides we present in the article “how Hide and Seek : How to find anyone online (and hide)” and our article on tinder investigations plus finally the article on “what can a hacker do with your email address”, you pretty much have the ammo to fully conduct your own personal online investigation into a username or email address, whether you choose to use an automated tool like UserSearch or not.
Using a new resource..checking scam dumps
A new resource has only recently been made available to the public, known as Scam Dumps. These are huge databases and collections of reverse search engines in one central location totally focused on collecting information on dodgy internet traders and romance scammers.

Half of the databases are populated by hard-working citizens like yourself. The other half is created by geeky computer scientists capturing data from various sources such as web crawling, the darknet, and various Deepnet APIs. The end result…a huge…huge collection of UserNames, Emails, CryptoCurrency addresses, and phone numbers of these dodgy individuals, for you to search. Sounds nice eh? Check this site out, they offer totally free searching plus a nifty free trial for some more advanced stuff.
They also let you search by profile picture on dating sites and social networks (known as reverse image searching). Not too shabby.
How to find someone on POF (plenty of fish) with a username or email?
API POF user lookup :
We saw no publicly accessible API as part of the user registration or user login screen. This is quite often a trick where websites use their own API to perform a username or email lookup to determine if a user/email is already registered. Most websites handle this code server-side, but we have seen some client-based (meaning we can see the code and thereby the API being called, which we can use to our advantage. If we could access this, we would have a programmatic way of checking, which has been exploited by some hackers historically.

POF email lookup via password reset :
We tested the password reset function, which is sometimes used by automated tools. You do not receive a message if an email account is valid/invalid or exists. It’s a blank response. Some websites will suggest that the email you have tried to reset does not exist. That response does not occur in this case, it’s a good design but bad for researchers like us.
POF email lookup using registration :
This is a trick where, during standard user registration, you can enter a used email (in this case, the email you are looking for), and the website will typically respond with ‘sorry that email is in use. That’s pretty nice, letting us know they are members of the website. However, POF has an odd way of dealing with this, which we believe is a bug. A lot of tools will automatically fill in registration forms and wait for a response like this to see if the user exists on the site.
Typically…
Typically, a website will call the database as soon as you enter an email address to determine if already in use (it saves you typing out the whole form to realize you just need to reset your own password). However, on POF, it allows you to fill out the full form as a new user and it then seems to reset the form and push you back to the start (if you try and register with an already used email account). We don’t know if this is a design flaw, or a purposeful tactic to discourage people from doing this.
POF user lookup using registration :
Similar to the trick for emails, by purposefully using a username that you are trying to look up, a website will call the server to see if the username exists.
We get a positive response during user registration and we can be provided with intelligence that this username is currently on the site.
Here is a picture of the response:
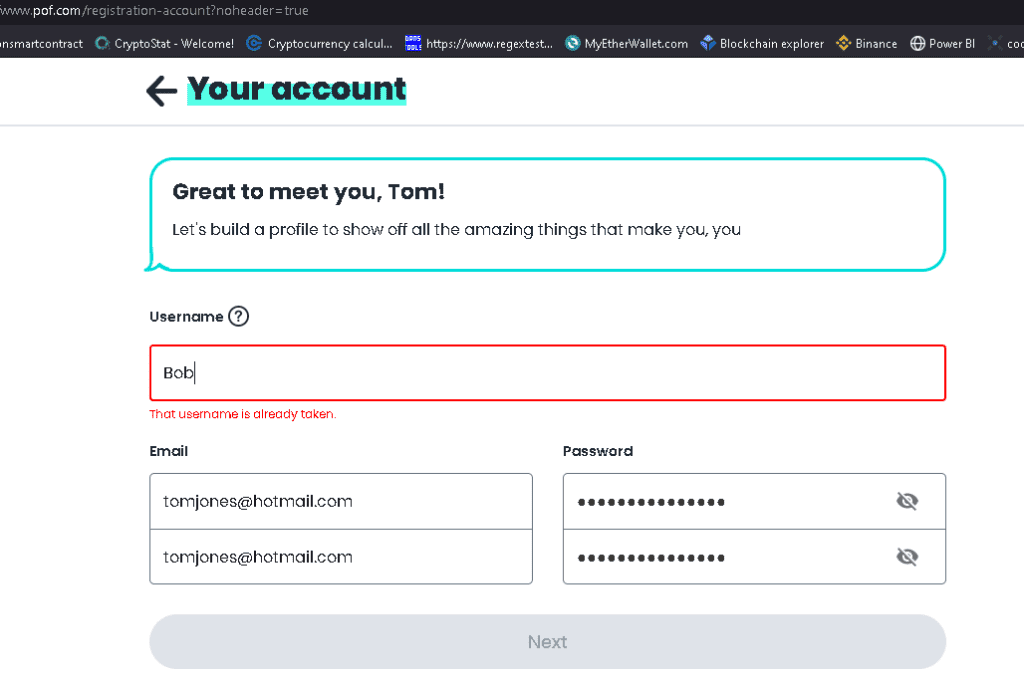
Plenty of fish will inform us during user registration that the user account ‘Bob’ already exists on POF. However, it will not inform us whether ‘tomjones@hotmail.com’ exists. If you keep filling in the required joining forms, it will eventually reset if you do not use a unique email address.
POF internal user lookup :
We logged in to POF to see if we can look for our user ‘bob’. Success, POF does allow full searching of usernames if you are a registered user. We can see pictures, preferences, and that they are married. Those pictures will come in handy with using some Reverse Image Searching later on.
POF lookup notes :
In conclusion, POF is pretty well locked down from the public side. The only glean of information it will release is the usage of a username, which still, depending on how confident in the uniqueness of the username, may be enough information for you to create a fake profile and login to POF.
How to find someone on Match (Match.com) with a username or email?
We follow the same process as we followed for POF to check for any public data leaks on match.
API Check: No API is publically accessible.
Password reset via email: Resets without informing you of the email existing.
Registration using email:
Once attempting to sign up, it will inform you an email is being used on the system. Not only that, it will allow what seems to be an unlimited amount of attempts at changing your email address to other possibilities..and then inform you if that email is being used. Someone with very basic web crawler skills could automate that function to pull out used emails on Match.com. Not sure of your target email? don’t worry, match offers unlimited retries (if not unlimited, then a lot)!
Username registration: not available.
We managed to sign up to match.com using a random email address (without email confirmation!) and random registration information. We can now fully browse all users and see their profile pictures and full profiles. What a treasure trove of information!
Match user lookup via URL :
Once logged into our fake account, we can see that each user is assigned a number rather than a username. E.G. “https://uk.match.com/d/profile-display/65456456466554“. A determined web crawler could download every single profile by incrementing the number.
How to do a Reddit User lookup?
Performing user lookups on Reddit is not difficult, the entire site is designed to be open. As per our usual test runs, this is what we found out:

User lookup via API :
This service provides a full itinerary of API access to their site, including username confirmation. They have a lot of documentation on how you can access this. This is why there are so many Reddit bots, but equally, they can be used to register users (and therefore determine if a user or email exists). We threw together a quick script just to test and it works rather well. We are not making it public because it can be used for mass user registrations.
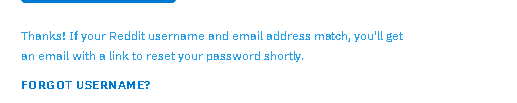
Password reset via email :
You need to get the Username & password correct, in order to cause a reset..plus they don’t tell you if either one exists. Nothing much we can do here.
Username reminds via email :
When we attempt to ‘remind’ ourselves of the username, we get a block to wait 10 minutes. On waiting patiently, again it will not confirm nor deny the existence of the username.
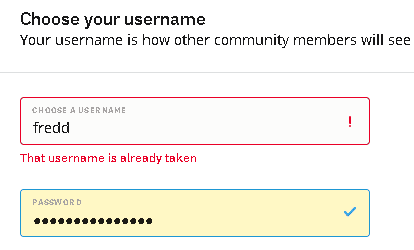
Username lookup via registration :
Success (if it can be classed that). On attempting to register an already used username, we are told so. Not very useful as we can simply check this via the site itself.
Finding Reddit users via URL :
The site makes it rather easy to find any user by username. You can simply use their inbuilt search function or if you want a more direct approach, you can enter it directly in the URL as so: “https://www.reddit.com/user/username/”. The cornerstone of Reddit is trying to find the email address, which does appear lockdown well. The only saving grace is the hope your target uses the same username on Reddit as they do on another social media account. From running a large reverse user lookup using a tool such, this can be determined rather quickly
How to do a Snapchat user and email lookup?
Snapchat is another social networking community but it’s mainly via phone access only and limited to phone users. However, we have found a number of ways to perform user lookups on Snapchat.

User lookup via URL :
Access to Snapchat user profiles is not directly public. However, it allows people to post stories and have a spotlight on the main page. You’ll see there are thousands of usernames available on here. You can quickly perform a URL lookup on these by using the following URL combinations:
1)https://story.snapchat.com/s/”yourUsernameHere”
A fly in the ointment here is if you enter a username within the above URL that does not exist, Snapchat will provide you a false-positive result, meaning they give the impression the user exists whilst they don’t as seen in the picture below.

Due to us reviewing the HTML code, there is a distinct difference in the title between a user with a public story vs non-public, so checks can still be automated.
Email lookup on Snapchat :
It looks like Snapchat has done the cardinal sin when it comes to logging into user accounts. If you simply try to log in but enter an email address that does not exist on their system, they will tell you there is no account! big mistake. They do not even require a bot checker should you attempt multiple email address lookups. As mentioned, hackers have built bots to mass query emails via these non-bot secured login pages to pull out the entire email list of the websites.
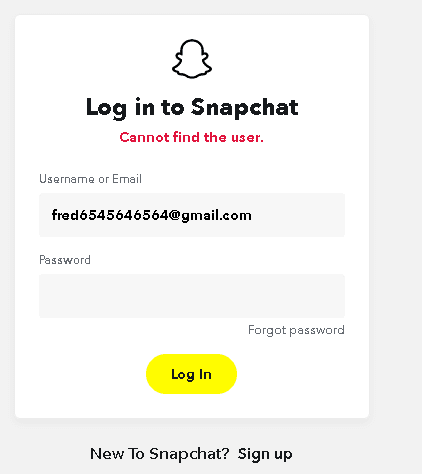
Username lookup on Snapchat :
Another cardinal sin by Snapchat, they allow quick and easy access to check username registrations. Should you attempt to create an account, they will inform you whether a username is being used on Snapchat or not. Again, no bot verification.

Phone Number Lookup on Snapchat :
Snapchat is not very high in our standards with data privacy it seems. In order to determine if a phone number is being used on Snapchat simply go to the password reset screen (https://accounts.snapchat.com/accounts/password_reset/phone). You don’t need to submit in order for them to inform you of this.
Cash App user lookups?
Cash App is a payment service that allows users to transfer money using their app. It’s mainly available in the USA and UK. We’ve checked this out, it has a few useful features for user lookups.

Cashapp user lookup via URL :
By design of the website, you are able to see via the URL, a user on this service. Simply type the URL followed by the username to look up if they are using the app, E.G. https://cash.app/$fred.
We checked the rest of this app, and it has no API, no password reset, and no registration. If you attempt to register, it instantly sends a code to the email or phone number in question, whether it exists or not.
How to do a Kik user Lookup?
Kik is a chat application that’s exclusively for mobile phones. We had to access the App therefore via our mobile phones.

Kik user logon screen :
On testing the logon screen, we entered a very common email address. It gave us the message that the password was wrong for the email address! Quite shocking given how easy bots use this for hacking. Useful for us, in performing an email lookup on Kik.
We then tried entering a random password for a made-up email, it let us know the email does not exist! It allowed us to do this, even if we did not enter a password.
Email lookups on Kik (password resets) :
They only let you access the password reset screen if you access the app via the phone (wrong!). They simply don’t advertise the password reset screen anywhere unless you are accessing it via phone.
Once you access the app on the phone, view the HTML and you’ll see a very insecure (no SSL) password reset page. You can then get the URL (http://ws.kik.com/p), access it via a browser on a computer and you will access it without issue (which makes deploying bots much easier). Did we say it has no SSL?
At least, we can presume it will not provide us any information that we can use for an email lookup like the logon screen, you would think? Surely not. If you simply enter a random long email that would not exist, they will politely tell you so. Another method of verifying email lookups on Kik.
How to do an Instagram user lookup?
Finding anyone on Instagram via manual user lookups is very easy, the site is nicely designed to be public and open. You won’t have issues finding people on here, the usernames are searchable via a URL lookup. They also have an internal username lookup you can use. Due to a lot of Instagram accounts being fronts for business or influencers, it’s in their interest to publicize their email on Instagram. We did the standard process as we have done for the others, but I don’t think you’ll have any trouble with Instagram user lookups.

Instagram URL user lookup :
Very simple, it’s literally “https://www.instagram.com/yourusername”. You don’t need to be logged in to see the profile. Users can set their profile to private of course, which will require you to log in and add them to view their content. If you’re just trying to ascertain whether that username is used on Instagram, it will tell you the profile is private.
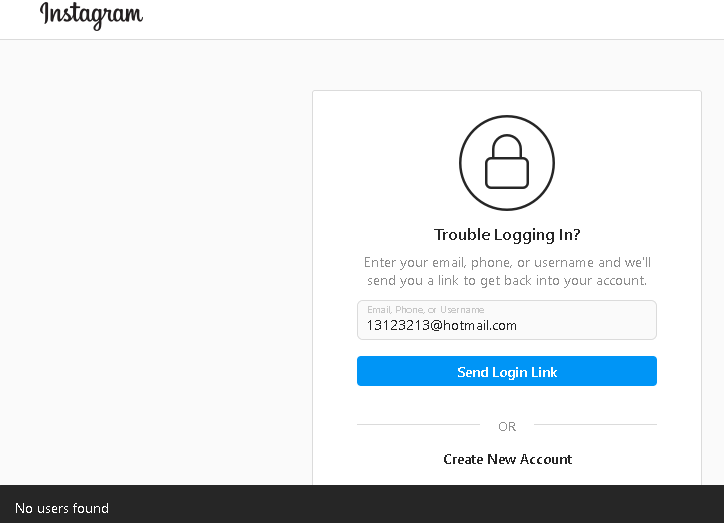
Instagram Email lookup (login screen) :
If you want to work out whether an email is currently being used on Instagram, they make it very easy. Too easy in fact, bordering on a security weakness. You can literally visit the login screen, enter the email address, and any random 8-character password. If the email is not used on Instagram, it will simply inform you.
We did this for phone numbers and usernames, all of which give open answers on whether those lookups are currently being used on Instagram.

Instagram HTML Review / Jquery Review / Public API – Reset Passwords :
Something a little more interesting caught our eye, mainly because we got bored that Instagram was so simple to perform user lookups. We checked out the password reset function. On testing a password reset, we noticed a pop-up saying ‘user does not exist.
Popup
A popup like this typically uses a client-based script (Java / Jquery / CGSI script) as you can see on the picture to the right (the black line pop-up). If the script is client-based, it means we can see it.
We started to review the browser console whilst re-running the request and discovered some interesting code. This code is usually a little more obfuscated (for security reasons).
Concealed API
By viewing the console inspector we see a POST query to
“https://www.instagram.com/accounts/account_recovery_send_ajax/“. If we expand this information and browse to the request, we will see they provide us with the variable names of the entered values. Very handy. What do we have here you ask? we have a fully accessible API to perform mass password requests (if scripted). Also, they seem to have 4 other values as part of the API, we can only assume one of them may have been ‘planned’ to be used for source verification? but by default they are blank and the API query accepts them blank. We created a quick API request via a free tool and can confirm it does not require the Captcha value nor the other values. Here is what we are looking at:
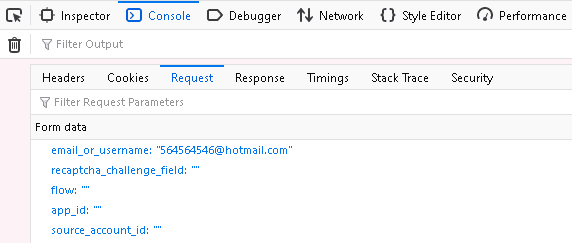
Advice :
We don’t suggest you use this method for your own online lookups (as resetting passwords inform users if nothing else!). It’s not often we find a perfect example of how to find publicly accessible (hidden) APIs to further your investigation. This methodology can be used to further your knowledge if nothing else.
Xbox Live Lookups, Minecraft Lookups, Github Lookups
I know we said that Xbox, Minecraft, and Github will also be reviewed, however, I think you’ve seen enough examples to repeat the process. We’ll probably do another article covering Xbox, Minecraft, and Github next, plus add a few new features we use.

Too much work?
It goes without saying, it takes a lot of work to manually perform user and email lookups. You may be able to check one website in 3-10 minutes, but there are a lot of social networks. But, you are reading an article on how to do it manually, soo…
This time investment is the main reason why we built our own lookup service for free, it helps us with our work and also helps over 500,000 people each month with theirs! The site was so useful for people we decided to expand this (with a significant cost to us!) and this is why we now offer an even more advanced version for $6.99 per month, with thousands of happy customers! We hope it continues to help and we are adding new websites to perform user lookups every week. Have some suggestions on the site, want new sites covered, or want a particular website reviewed in the next article? simply drop us an email at support@usersearch.org.