It’s no secret that the world we live in revolves around information. And this information, playing a major role in our lives, is everywhere. But do you know where to look?
With just a few taps on your keyboard, you can quickly check on someone or something. Computers and phones have made our lives easy. This is simply because it has enabled seamless internet surfing through search engines. And all these are possible thanks to the content provided on OSINT websites.
In this article, we’re covering:
- What OSINT entails
- How open source intelligence is used
- Open source Intelligence techniques
- OSINT tools, and
- Finally, the OSINT courses.
So, keep reading, and let’s begin! Already a seasoned OSINT’er? hopefully, you may just pick up a few new hints.
What Is Open Source Intelligence?
OSINT stands for “open-source intelligence,” which refers to data and information legally gathered from free published available sources, usually the OSINT websites. Or in simple terms, it is data and information readily available to the public, and there is no limitation on what can be found on google or the surface web.
Similarly, OSNIT is insights collected from analyzing public data sources like TV and radio broadcasts, OSINT websites, or social media platforms. Furthermore, the data retrieved can be in the form of text, images, audio formats, webinars, and video footage.
Information is considered open source when it meets any of the following criteria:
- Available publicly on request, e.g., census data
- Available publicly on purchases or subscription
- Can be obtained easily by visiting places open to the public
- Broadcasted or published in public to an audience
- Made available at a public meeting
Now that we know the basics of OSINT let’s dive into how open-source intelligence is used.
How Is Open Source Intelligence Used?

Well, OSINT cyber security experts use open-source intelligence for two crucial reasons:
1. Penetration Testing and Ethical Hacking
OSINT analysts or cyber security experts use penetration testing. This helps them discover possible security vulnerabilities on a network, computer system, or web application.
In fact, the commonly uncovered weaknesses by the cyber security experts include:
- Data leaks that accidentally reveal confidential information to the public
- Exposed assets such as devices names, IP addresses, and networks
- Unpatched software, e.g., websites using old versions of CMS products
- Open ports and unsecured devices connected to the internet
2. Determining External Threats
With much information available on OSINT websites, hackers can easily attack their targets. Therefore, open-source intelligence helps cyber security experts to address the cyber-attacks, thus dealing with these threats. OSINT helps identify current cyber threats and prevent attackers from attacking a network or an organization.

Identifying and comparing multiple data points is essential to ensuring advanced security. This is simply because it helps analysts vindicate a threat before it becomes an attack. Furthermore, security experts search deeper internet layers to determine external threats.
For instance, open-source intelligence analysts may access the deep and dark web. This helps to collect and analyze intelligence used for data leaks by hackers. As a result, it improves analysts’ potential to enhance security against potential future attacks.
Keep in mind that OSINT is important in optimizing OPSEC. This is a process of determining friendly actions that may be convenient to identify a potential attacker. This is a viable process provided they are analyzed appropriately.
What types of osint Techniques are there?
First, what is the OSINT technique?
For starters, it is important to develop a strategy and have a framework that is all-set for using open source intelligence. It is necessary because the volume of information available in open sources is quite overwhelming. The fact is, you will encounter tons of information that might drive you away from your goal. Therefore, it is recommended that you know what you want to achieve and put focus precisely to attain the set tasks.
For instance, if your goal is to identify and improve vulnerabilities in your network, that’s where you should specifically focus all your energy. In addition, it is important to identify a set of tools and techniques for gathering and analyzing open-source intelligence.
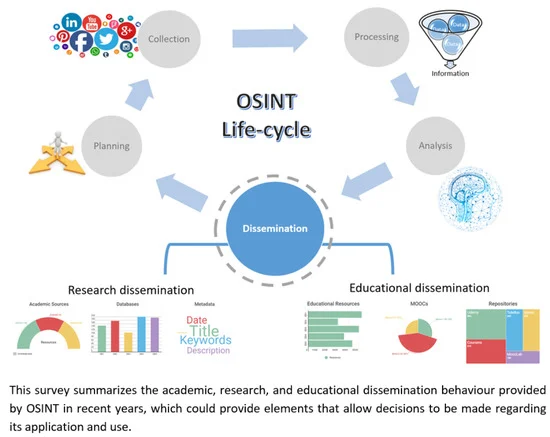
To meet their organizational needs, OSINT cyber security analysts need to adopt suitable techniques. And So, the Open Web Application Security Project (OWASP) shows Five OSINT techniques to use:
- Source Identification-Identify where to gather data regarding a specific task.
- Harvesting- Collect information relevant to your search from the source identified.
- Data Processing- Process andextract relevant details from the identified source.
- Analysis- Contrast the processed data with multiple sources.
- Reporting- Design a report on your findings.
OSINT techniques can be classified into two categories: Passive collection and Active collection.
a. Passive collection
This technique often involves collecting information about a specific network or device without necessarily engaging with the system. OSINT cyber security experts rely on third-party information using passive collection tools such as Wireshark, which analyzes traffic in a network in real-time for Mac, Unix, Linux, and Windows systems. Passive collection tools piece together the different OSINT online data points to locate and map patterns on a behavior of a network.

b. Active collection
This technique engages directly with the target system giving timely and more accurate information. OSINT cyber security analysts use active recon tools such as Nmap, which is an OSINT online network discovery tool that provides a highly detailed view of a network’s security.
What are the best Open Source Intelligence (osint) Tools Online?
Before we dive into discussing the best OSINT tools, it is essential to note that there are various free and paid OSINT tools available. These tools can be used to:
- Find email address and verification.
- Identifying wireless networks and analyzing packets.
- Searching phone numbers.
- Analyzing images.
- For investigating people and finding out their identities.
- Metadata and code searching.
- Mapping and researching geospatial.
- Social media accounts linking.
- Find the user in the forum
Now let’s take a look at some useful OSINT tools.
1. TheHarvester
TheHarvester is a penetration testing tool used to collect information. For example, you can collect info about emails (find email address), subdomains, open ports, banners, employee names, and hosts.
In addition, it collects these data from various public sources, such as search engines, SHODAN computer databases, and PGP key servers.
2. UserSearch
UserSearch is the largest free, reverse lookup tool online. It has an exhaustive list of services, such as lookup for emails, forum users, crypto site users, dating site lookups, and adult website lookups. It can even analyze a webpage and pull out all the emails on that page. Furthermore, they are working on a new advanced version that has even more features (still in development but you can sign up to have access).
They let you search for free against over 600+ websites, which is the largest collection online.
3. Scam Search
ScamSearch is an amazing tool, that offers the largest, free, Global Database of scams and scammer details. They harvest reported Scammer details from government websites, public reports, and other areas. They push all this data together to make sense of it, and let the public quickly search it within seconds. To date, they have over 4 million recorded, live scammer details, recording their email address, username, real name, phone number, bitcoin address, and a synopsis of how they are trying to scam people. Amazing.
Advanced Searching: They even have a system where you can fill in a table of someone you are looking for by crypto address, email, username, or phone number. They will then check all new reports coming in and email you when a report comes in on your target! What’s more, if you are concerned someone is friendly using your brand name or identity to conduct scams, you can monitor reports for your own details to help track down who is using your details.
2. Babel X
This is a multilingual internet search tool used for finding information available in public. This means finding info from sources such as social media, forums (find user on a forum), blogs, and news sites in over 200 different languages. One major upside of this tool is that it is designed to filter relevant information into various groups.
3. GHunt
If you’re looking to find data related to Google accounts, such as owner’s name, YouTube, Google ID, Photos, and Maps, GHunt is the ideal tool to use. Perhaps, this is a well-crafted OSINT tool specially designed to deliver the best results.
4. Maltego
Maltego is an OSINT tool that has uses such as; finding connections between data instances and generating a map. In fact, it helps to figure out “Find user on the forum” by searching through social media profiles, which is perfect for investigations.
5. Recon-ng
If you want to perform web-based reconnaissance, then Recon-ng is the best tool to go with. This tool is, in fact, a gathering open-source intelligence tool.
6. Shodan
Shodan is a search engine that is used to gather intelligence data from various IoT devices such as routers, servers, and webcams.
7. Spiderfoot
This is another reconnaissance OSINT tool. Spiderfoot is specially designed to query more than 100 data sources (OSINT) automatically. By doing so, it helps collect information on IP addresses, email addresses, domain names, etc.
8. Intelligence X
Intelligence X is an OSINT tool used as a search engine and data archive. In fact, it performs a search for data leaks, Tor, I2P, and the public web using an email address, CIDR, domain, bitcoin address, and IP.
9. Intel Owl
Collecting threat intelligence information on a specific file, a domain, or an IP through a single API request is essential to enhancing security. The perfect tool to help with this would be Intel Owl.
10. TinEye
This OSINT tool is used as an image recognition tool.
11. Searchcode
This tool is used as a source code engine. It helps with listing API documentation, open-source repositories (free software), and code snippets.
12 Social Mapper
Social Mapper is a tool that matches social media profiles. In fact, this tool can help you find users across various sites on a large scale using facial recognition.
13. ZMap
For those of you looking to carry out internet-wide network surveys, then ZMap is an ideal OSINT network tool to use.
What is the OSINT Framework?
Having OSNIT tools and a set of OSINT techniques is a great place to start. However, adding an OSINT framework will actually make it much better and highly recommended to use.
So, let’s take a look at what the OSINT framework is.
The OSINT Framework refers to a cybersecurity structure with a collection of OSINT technologies. These technologies can be used to find information quickly and simply on a specific target. Basically, it is a web-based platform that allows users to browse OSINT tools such as Maltego, Virtual machines, etc., on diversified themes and goals based on their needs.
You can browse the OSINT tree easily as it provides a perfect classification of all existing intelligence sources.
Below you can find an OSINT framework structure.

From the above image, you can see that different category are given in the shape of a tree. Its ranges from simple stuff like username and email address to more detailed info like domain name, IP address, etc.
Also, by simply clicking on any of the themes, a sub-category of convenient resources pops up.
Additionally, if you are searching for an email address, phone records, or IP address, you can easily find all of them in categorized one place. This, therefore, makes the OSINT framework very vital in OSINT cyber security.
Key takeaways on OSINT Framework:
Once you visit the OSINT framework website, you can find the following indicators from the top right corner of your screen:
(T)- denotes a link to a tool that must be installed and run locally
(D)- GoogleDork/Google hacking
(R)- Requires registration
(M)- denotes a URL that contains the search term. Also, the URL itself must be edited manually
What are the best OSINT Courses Available?
Hey, are you ready to take Open Source Intelligence learning to a higher notch? Well, if the answer is yes, check out these fantastic OSINT courses.
a. SEC487: Open-Source Intelligence (OSINT) Gathering and Analysis
Without doubt, this is an excellent place to start if you are looking to sharpen your techniques on finding data on the internet. You can register for SEC487. This is a foundational course in open-source intelligence (OSINT) gathering and analysis.
In fact, this course aims at providing learners with fundamental principles of OSINT. It also sets you to be successful in your career pathways, be it as an:
- OSINT Cyber security defender,
- threat intelligence analyst, private investigator,
- intelligence analyst, insurance fraud investigator, or
- anyone curious to learn more on OSINT.
b. NPCC Cybercrime (OSINT) Training Programme
The NPCC offers a cybercrime training program to law enforcement in England and Wales. It teaches skills required to adequately respond to a cybercrime case and investigate it effectively.
Additionally, it helps you learn how to prosecute offenders. You can also help individuals reform from cybercrime activities to better productive pathways. Furthermore, this course gives staff technical skills to protect and advise organizations and individuals on OSINT cyber security. This helps them be able to protect themselves from cybercrime.
c. OSINT: Open-Source Intelligence.
For $49.99, you can purchase this guide. With this course, you will:
- Have a better understanding of OSINT,
- How to perform it,
- Learn OSINT from a hacker’s point of view,
- Setting up a virtual lab, and
- Better ways to protect yourself.
Generally, this course will show you how hackers and investigators use OSINT tools and why.
How to self Self-Teach OSINT?
This is not a course, but it’s worth a mention. If you are good at learning new crafts by yourself, this is a great way to learn OSINT online. In fact, you can use published material i.e, OSINT related websites, or watch some YouTube tutorials.
More OSINT Resources?
Overall, we have covered what OSINT is and its fundamentals. And so, I hope that by the end of your reading, you have picked up one or two ideas (s) on the concept of OSINT. Whether you’re majoring in OSINT cyber security or you’re fond of reading such posts, visit the provided links on OSINT websites to get more insights on the same.
Did you find this article useful? if so, you may be interested in: